Three Israeli Contractors Behind Iron Dome Were Hit By Chinese Hackers

Image by Getty Images
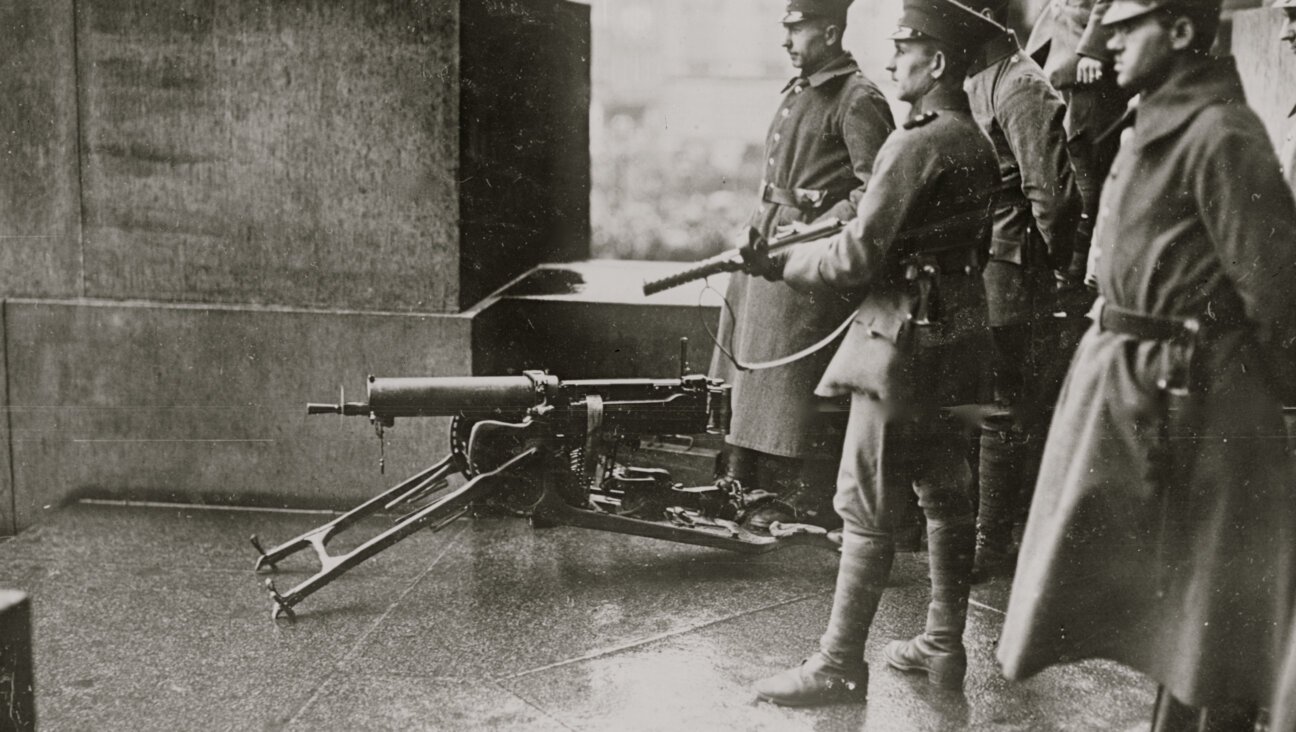
Three Israeli defense contractors behind the Iron Dome missile shield and related systems were robbed of hundreds of documents by hackers linked to the Chinese government starting in 2011, a U.S.-based computer forensics expert said on Tuesday.
Comment Crew, as the hacking group is known, stole designs for Israeli rocket systems in a spree of attacks during 2011 and 2012, Joseph Drissel, chief executive of Cyber Engineering Services (CyberESI), said in a phone interview.
The targets of the online attacks were top military contractors Elisra Group, Israel Aerospace Industries, and Rafael Advanced Defense Systems. The companies built the system that now partially insulates Israel from rocket barrages fired from the Gaza Strip.
Israeli and U.S. officials have said Iron Dome systems are responsible for shooting down more than 90 percent of the rockets they have engaged, while ignoring missiles on a trajectory to fall wide. That accounts for about a fifth of the rockets Israel has said Palestinian militants have fired into the country during the Gaza Strip crisis.
Krebs on Security, a blog operated by former Washington Post security reporter Brian Krebs, first reported details of the intrusions on Tuesday after being briefed by Drissel on his company’s findings.
Four years ago, Drissel founded CyberESI, a threat intelligence consulting firm based in Columbia, Maryland. That came after a decade in the computer forensics lab of the Defense Cyber Crime Center (DC3), an arm of the U.S. Air Force, where he was acting section chief.
His company, which includes former colleagues from his U.S. Defense Department forensic lab, traced the intrusions into Israeli contractors and identified more than 700 stolen emails, documents and manuals pertaining to development of the Iron Dome project and other missile projects.
“‘Comment Crew’ is so named for a very specific reason: They insert malware with hidden comments on various public Web pages they control and use those sites as command and control centers to download stolen documents,” Drissel said.
CyberESI identified these sites and was able to grab evidence of the stolen documents before Comment Crew could cover their virtual tracks, he said.
Drissel said he was disclosing the attacks only now, after years of seeking unsuccessfully to persuade the affected companies and U.S. and Israeli government authorities to address both the security issues that led to the breaches and to take stock of what specific weapon systems may have been compromised.
In May, the U.S. Justice Department indicted five Chinese military officers who allegedly belonged to Comment Crew, also known as Unit 61398 and based in Shanghai. They were accused of hacking into the networks of U.S. Steel Corp, Toshiba Corp’s Westinghouse Electric unit and four other U.S. companies in order to steal trade secrets.
Allegations of hacking and other espionage have strained ties between China and the United States, with Beijing denying last year that it had set up a special military unit to conduct such activity. China retaliated by shutting down a bilateral working group on cyber security.
Two of the Israeli companies named by Drissel declined to comment on the computer security expert’s revelations.
An official at the third company, Rafael Advanced Defense Systems, who declined to be identified by name, said of the report: “Rafael does not recall such an incident. Rafael’s databases, including its air defense databases, are extremely well protected.”
A former senior Israeli military official said assertions that these key defense contractors had been hacked would fit with a pattern of military and industrial espionage around the globe.
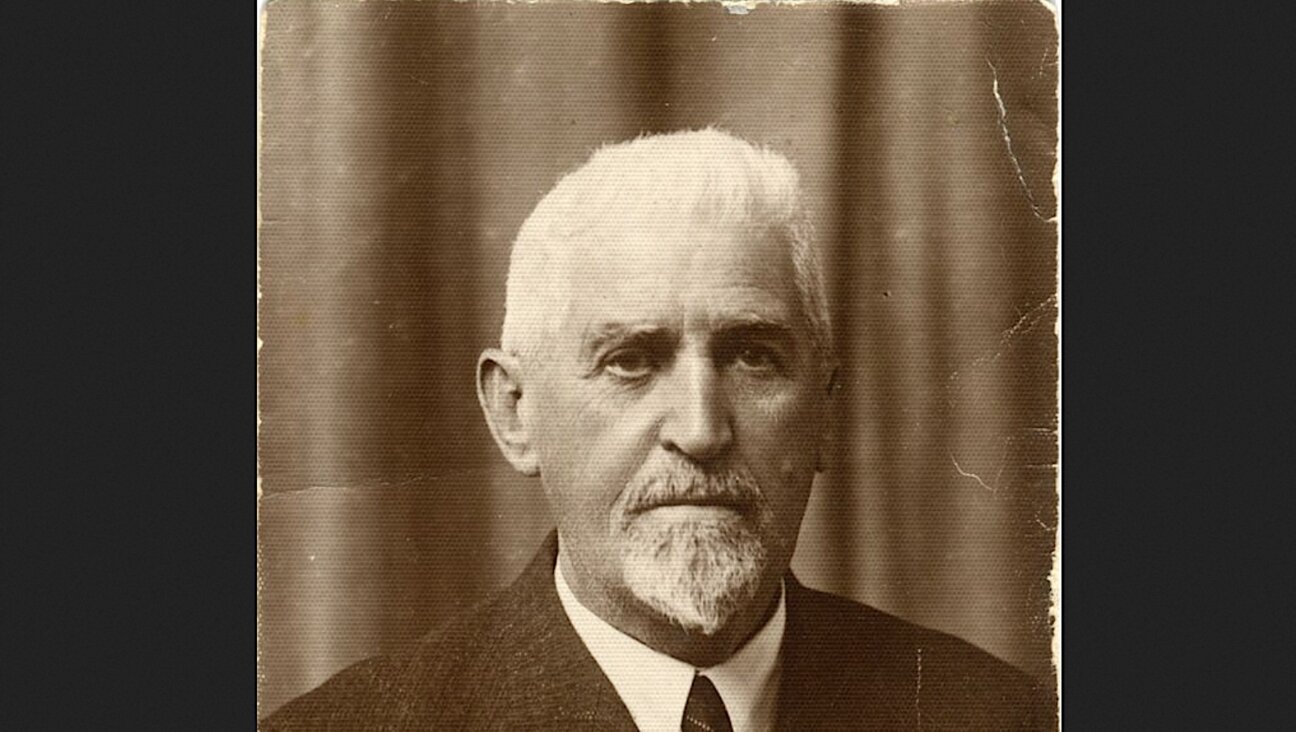
“The Chinese have been doing that to all defense contractors in the West, so if this really happened, we are not alone,” said Uzi Rubin, a former head of missile defense at Israel’s Defense Ministry and now head of the Rubicon consultancy firm.
Drissel said stolen materials recovered by his company included specifications for the Arrow III system and other ballistic missile defenses. Much of the technology for these systems was developed by Boeing and other contractors for use in U.S. weapons.
Rubin speculated that if the Comment Crew hacking group’s purpose was to steal the missile system plans, it was likely that China wanted to obtain technology on the cheap rather that reselling it to other nations.
“If the Chinese really did it, maybe we shall see a Chinese Iron Dome in the future,” he told Reuters. “It is said that imitation is the sincerest form of a compliment.”
Chinese officials were not immediately available for comment.