IDF Launches Campaign Against Hamas Catfishing Apps

Graphic by Angelie Zaslavsky
JERUSALEM (JTA) — The Israel Defense Forces has launched a campaign to prevent its soldiers from being tricked by hackers from terrorist groups attempting to install spyware on their cell phones.
The IDF announced on Tuesday that it had launched Operation Broken Heart, so named because operatives pose on social media as attractive females to convince the soldiers to download infected applications for dating websites, as well as another about the FIFA World Cup.
This is not the first time that Hamas and other terror groups have attempted to infiltrate the IDF via soldiers’ cellphones and social networks. A previous campaign known as Operation Hunters Battle exposed the false identities terror groups used to attract soldiers, in order to raise soldiers’ awareness of the phenomenon and the importance of reporting incidents when they occur.
Over 100 soldiers have been fooled into downloading the infected apps in the last six months, according to the IDF. Under the plot, the operatives befriended the soldiers on social media and then convinced them to download an infected app to their cellphone, giving the terrorists access to all of the information of their phones as well as turning on the recording devices and cameras on the phones.
The names of the apps are Glancelove, Winkchat, and Golden Cup. The apps were downloaded from the Google Store.
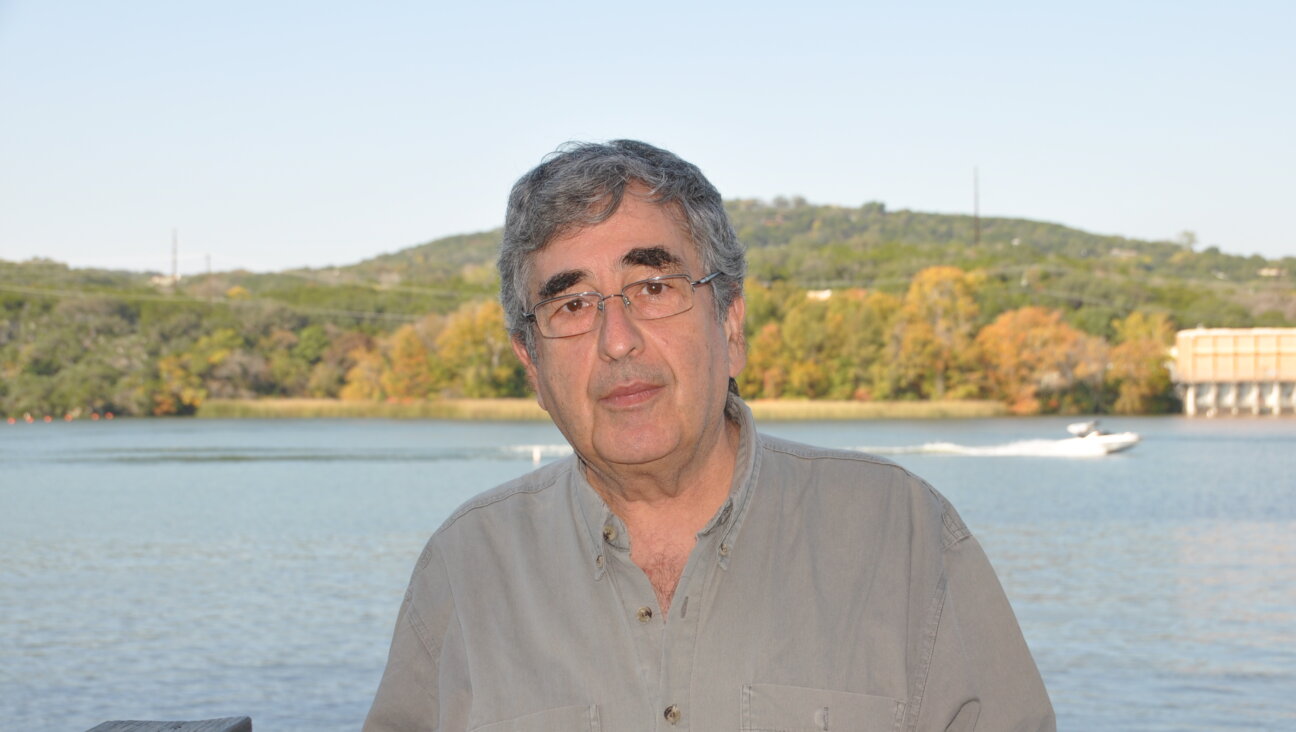
Hello, fellow Forward reader! I’m Joel Brown, a Forward reader and supporter for more than 15 years, and currently the chair of the board of directors.
I’m an avid Forward reader because it ticks so many of my essential boxes: excellent journalism, Jewish focus and diverse viewpoints. In today’s political climate, what I most appreciate is the Forward’s independence — made possible by the generosity of its membership.
The Forward is committed to bringing you unbiased, nuanced Jewish news. From my position as board chair, I see an exciting future as we expand our position as the definitive independent voice of contemporary American Judaism.
— Joel Brown, Forward board chair