Cyber Warfare Is Real — Should We Blame the U.S. and Israel For Starting It?

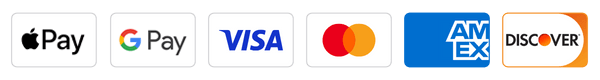
Image by Magnolia Pictures
In late 2009, something almost laughably scary started happening at the Natanz nuclear facility in Iran: centrifuges — slim cylinders containing powerful rotors used to enrich uranium — began exploding.
It wasn’t clear why. Or how. The operating data for the impacted centrifuges gave the impression they were functioning at normal levels, and when technicians monitoring that data received visual or aural clues that not all was well, the emergency shutdown system refused to initiate.
In June of 2010, Sergey Ulasen, an employee of a Belarusian internet security company, was asked to look at an Iranian customer’s computer, which was malfunctioning in unusual ways. The scale and complexity of the malware impacting the device went far beyond anything Ulasen had previously seen.
That malware, dubbed Stuxnet, is the subject of the new documentary “Zero Days” by Alex Gibney.
It’s a clever title, a reference to zero-day exploits, extremely rare hacking weapons that capitalize on software vulnerabilities gone unnoticed by the software’s manufacturer, allowing the malware to operate with remarkable rapidity. (On average, antivirus researchers discover 12 million pieces of malware each year, and fewer than a dozen with zero-day exploits; Stuxnet had four.) It also evokes the panic-causing language attached to earth-shattering events — ground zero, patient zero — presaging Gibney’s overarching message: cyberwarfare will change everything, it’s already arrived, and we have zero days to spare in preparing for it.
The story of Stuxnet illustrates that point in ways that were, for its creators, surely unintentional. (While no party has claimed the creation of Stuxnet, Gibney, the Oscar-winning director of “The Corporation,” “Going Clear” and “Taxi to the Dark Side,” subscribes to the most popular theory, which is that it was a collaboration between the intelligence branches of the United States and Israeli governments.) Stuxnet was sophisticated, targeting the industrial systems that helped operate Natanz with remarkable specificity. Its success in altering those systems — an unnamed source in Gibney’s film explains that Stuxnet’s entire mission, or “payload,” was to alter instructions sent to centrifuges about how quickly to rotate, causing them to explode by either going either too fast or too slow — demonstrates the potential of cyber weapons to execute difficult-to-trace attacks on military, industrial, and civilian targets.
The backlash following Stuxnet’s discovery makes a most sinister point about the current lack of regulation regarding the use of cyber weapons. As the code became public, providing an unintentional guide to the organization of a large-scale cyber attack, governments scrambled to boost cyber security. Iran created one of the world’s largest cyber armies. And in the United States, the Department of Homeland Security (DHS) leapt to secure U.S. targets against the program; “Zero Days” indicates the DHS had no knowledge of Stuxnet’s development. Gibney makes use of this communication gap, suggesting that a point of true alarm should be reached when a government deploys a weapon not only without developing a defense against it, but also without alerting those responsible for defense to the weapon’s existence.
He’s likely right about that, and he’s certainly right about his closing point, which is that just like the techniques of land, sea, and air-based warfare, cyber warfare needs to exist in a system of internationally agreed-upon and observed rules. Unfortunately, the film is both too sensationalistic and too biased to make those points as clearly as they deserve.
To start with, Gibney spends a great deal of screen time documenting the difficulty of finding U.S. government officials willing to speak on the record about Stuxnet. His frustration at that effort’s futility comes across as petulant, not urgent. Once he locates a source, he expends a great deal of effort to “conceal” that source’s identity, depicting her through a bizarre, distracting digital filter. The filter is unsuccessful — the face it creates is an only mildly-obscured version of that of the woman speaking — and, it turns out, pointless, as the woman is revealed to be an actress reciting the amalgamated testimony of a number of government sources. By sifting his primary American governmental sources through this clumsy cinematic and narrative technique, Gibney strays too far into spy-movie territory, and he distills the impact of the sources’ revelations.
Gibney also errs by choosing not to feature a single voice in the film offering a perspective that differs from his own, and, despite the fact that the history of Stuxnet is still a matter of allegation rather than absolute certainty, treats the story of its development, release, and uncovering as one of absolute fact. His lack of inquiry into other sides to the story is most evident when it comes to the misstep that unmasked Stuxnet, which had been operating in successful anonymity: at some point, a version of the program was released that stepped up the aggressiveness of its attacks against computers infected with it, alerting the owners of those computers to its existence. Gibney’s American sources agree that the fault lies with Israel, which they vaguely assert meddled with the program and launched it without seeking U.S. approval. No Israeli voices confirm this story, and none of Gibney’s talking heads suggest that even if it is accurate, the United States might have had some responsibility to guard such a powerful program against misuse by its allies.
Are international treaties providing some regulation over the uses of cyber weapons necessary? Absolutely. Are the capabilities of such weapons, as demonstrated by Stuxnet, both profound and too far removed from the realm of public accountability and debate? Probably. It’s unfortunate that such important questions are being introduced, to many, by a film that makes so few attempts to proceed with a genuinely searching eye.
Talya Zax is the Forward’s summer culture fellow. Contact her at [email protected] or on Twitter, @TalyaZax
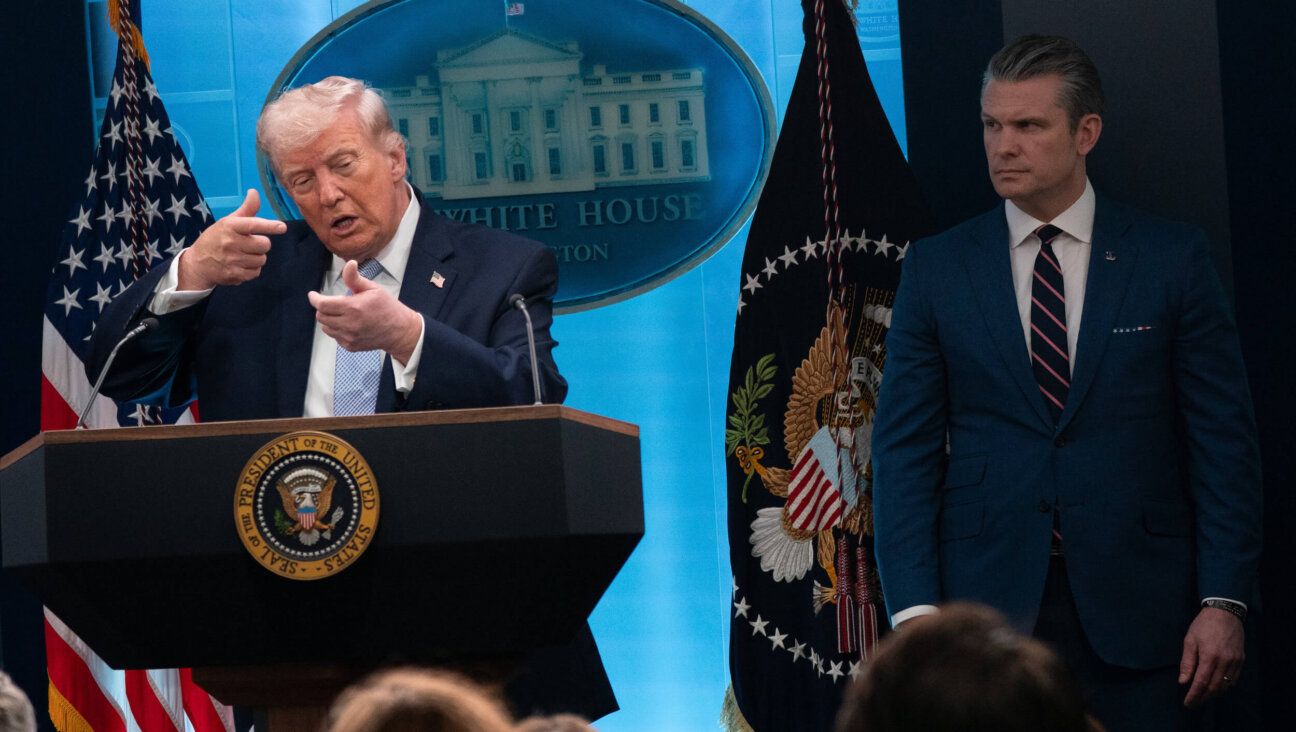
This is a moment of great uncertainty. Here’s what you can do about it.
We hope you appreciated this article. Before you go, we’d like to ask you to please support the Forward’s independent Jewish news. All donations are still being matched by the Forward Board - up to $100,000 until April 24.
This is a moment of great uncertainty for the news media, for the Jewish people, and for our sacred democracy. It is a time of confusion and declining trust in public institutions. An era in which we need humans to report facts, conduct investigations that hold power to account, tell stories that matter and share honest discourse on all that divides us.
With no paywall or subscriptions, the Forward is entirely supported by readers like you. Every dollar you give is invested in the future of the Forward — and telling the American Jewish story fully and fairly.
The Forward doesn’t rely on funding from institutions like governments or your local Jewish federation. There are thousands of readers like you who give us $18 or $36 or $100 each month or year.